VMware: Recover vCenter Single Sign On (SSO) master password
 During the installation of the VMware vSphere Web Client I had to provide vCenter Single Sign On Information. Since no additional accounts / groups where granted SSO admin privileges (see VMware vSphere 5.1 Documentation Center) the only account that had sufficient privileges was the default SSO admin user admin@System-Domain. The credentials of this account are provided during installation of the vCenter Single Sign On Service.
During the installation of the VMware vSphere Web Client I had to provide vCenter Single Sign On Information. Since no additional accounts / groups where granted SSO admin privileges (see VMware vSphere 5.1 Documentation Center) the only account that had sufficient privileges was the default SSO admin user admin@System-Domain. The credentials of this account are provided during installation of the vCenter Single Sign On Service.
Unfortunately the password of the default SSO admin account was unknown. In this article I’ll explain how to change the password of the default SSO admin account.
Master password
VMware provides us with a solution to reset the password of the default SSO admin account (KB2034608) but it requires the master password. The master password is set during installation, the password provided for the default SSO admin account is used as master password, but it is not the same password as the default SSO admin account.
Although we can change the password of the default SSO admin account (admin@System-Domain), changing the master password is not possible (or supported). After the password of the default SSO admin account is changed the master password is still unusable. 
Default SSO admin account
The vCenter Single Sign On Service stores all data in a databases, including the principals. The credentials of the default SSO admin account are stored in the IMS_PRINCIPAL table. One of the stored properties is a SSHA-256 (salted) hashed password. Changing the password is as easy as replacing the hash (also known as pass the hash) from a clean vCenter SSO service installation.
Schubis wrote a (german) article how to generate a new hash and how to replace it in your existing vCenter SSO setup. Unfortunately this requires you to built a lab environment with a SQL server and vCenter Single Sign On service, which is time consuming. Since you can change the password afterwards, I might as well provide you with some pre-created hashes:
Passw0rd!
{SSHA256}B6HO7UNHVi5fglh1RpJXX4z1maGJ9lcicTVcy94ztsmzAekseg==
VMware1234!
{SSHA256}KGOnPYya2qwhF9w4xK157EZZ/RqIxParohltZWU7h2T/VGjNRA==
Recover access
If you need to recover access of the default SSO admin account please follow the following three steps:
1. Reset password to temporary password
Connect to the SQL database (default is RSA) and execute the statement below to reset the password of the default SSO admin account to Password!
UPDATE
[Dbo]. [IMS_PRINCIPAL]
SET
[PASSWORD] = '{SSHA256}B6HO7UNHVi5fglh1RpJXX4z1maGJ9lcicTVcy94ztsmzAekseg=='
WHERE
LOGINUID = 'admin'
AND
PRINCIPAL_IS_DESCRIPTION = 'admin'
2. Restart vCenter SSO service
Restart the service “vCenter Single Sign On” to apply the changes.

3. Change the password the default SSO Admin account
Connect to the VMware vSphere Web Client and authenticate with the new default SSO credentials (username : admin@System-Domain and password : Passw0rd! ).
Navigate to Home > Administration > SSO Users and Groups
Select the default SSO admin account > Action > Edit User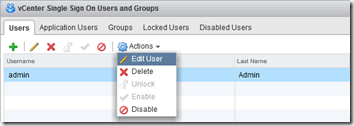
Change the password of the default SSO admin account to your preferred password

Please avoid the use of special characters in your SSO administrator password like (^ * $ ; ” ’ ) < > & | \ _”), non-ASCII characters and trailing “ “ space as the vCenter SSO service cant’ handle it (KB2035820)!
Lessons learned
To avoid this situation in the future I wrote down some lessons I learned. Although their very obvious, it’s good to keep them in mind.
- Always store the master password in a safe location
- Grant additional users / groups administrative SSO admin privileges
- Preferably add an Active Directory integrated group in __Administrators__
- Database administrators (DBA) can get access to your VMware vCenter by replacing a simple hash
.
Was once an enthusiastic PepperByte employee but is now working at Citrix. His blogs are still valuable to us and we hope to you too.
